RSA encryption calculator takes center stage as we embark on a journey to decipher the complexities of secure communication. Step into a world where cryptography and mathematics intertwine, unveiling the secrets that safeguard our digital exchanges.
RSA encryption, named after its brilliant creators Rivest, Shamir, and Adleman, stands as a pillar of modern cryptography. With its robust algorithm and wide-ranging applications, it has become an indispensable tool for protecting sensitive data and ensuring the privacy of our online interactions.
RSA Encryption Process

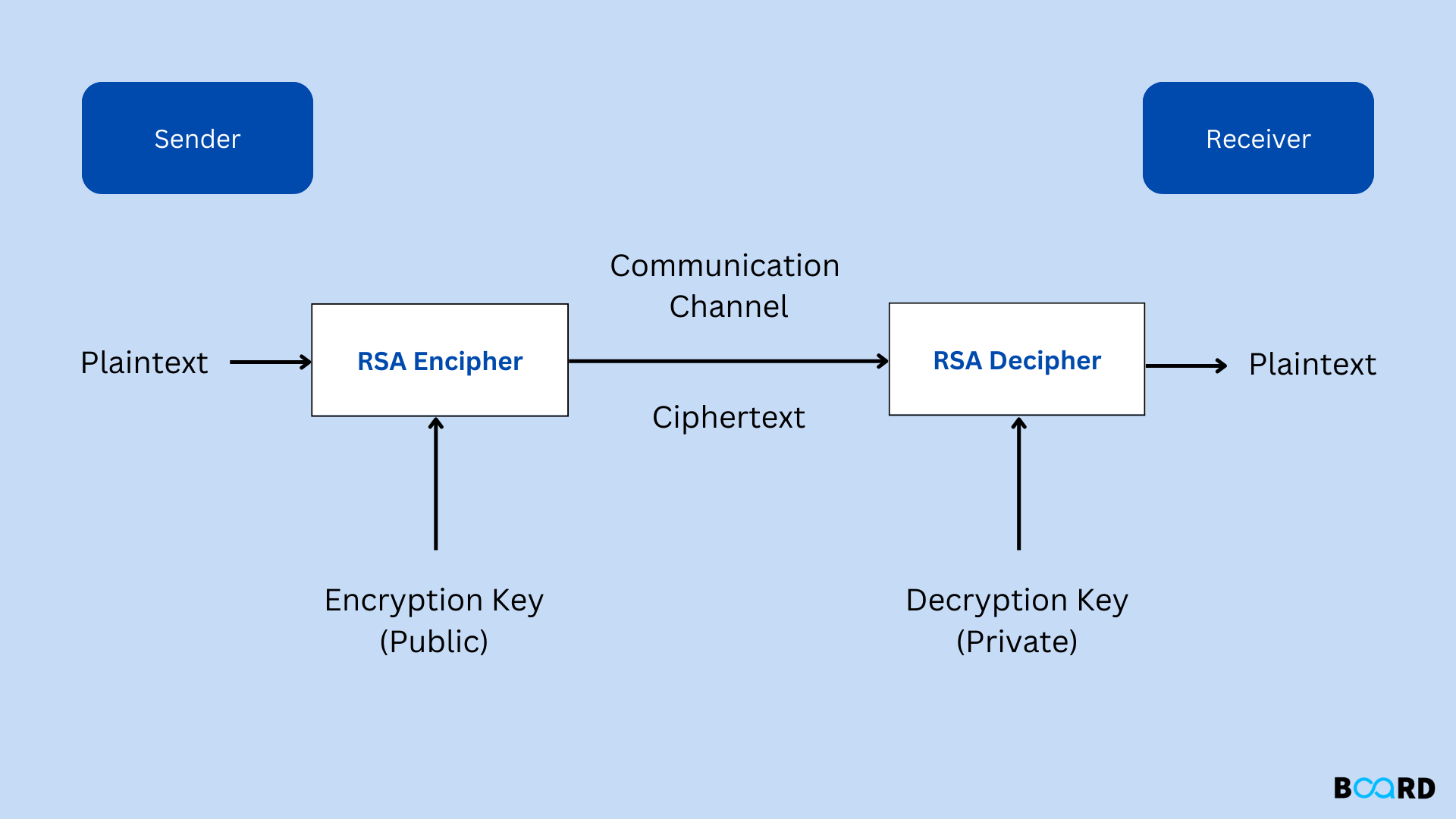
RSA encryption is an asymmetric cryptographic algorithm that uses a public key for encryption and a private key for decryption. It is widely used in secure communication, such as in SSL/TLS protocols and digital signatures.
The RSA encryption process involves the following steps:
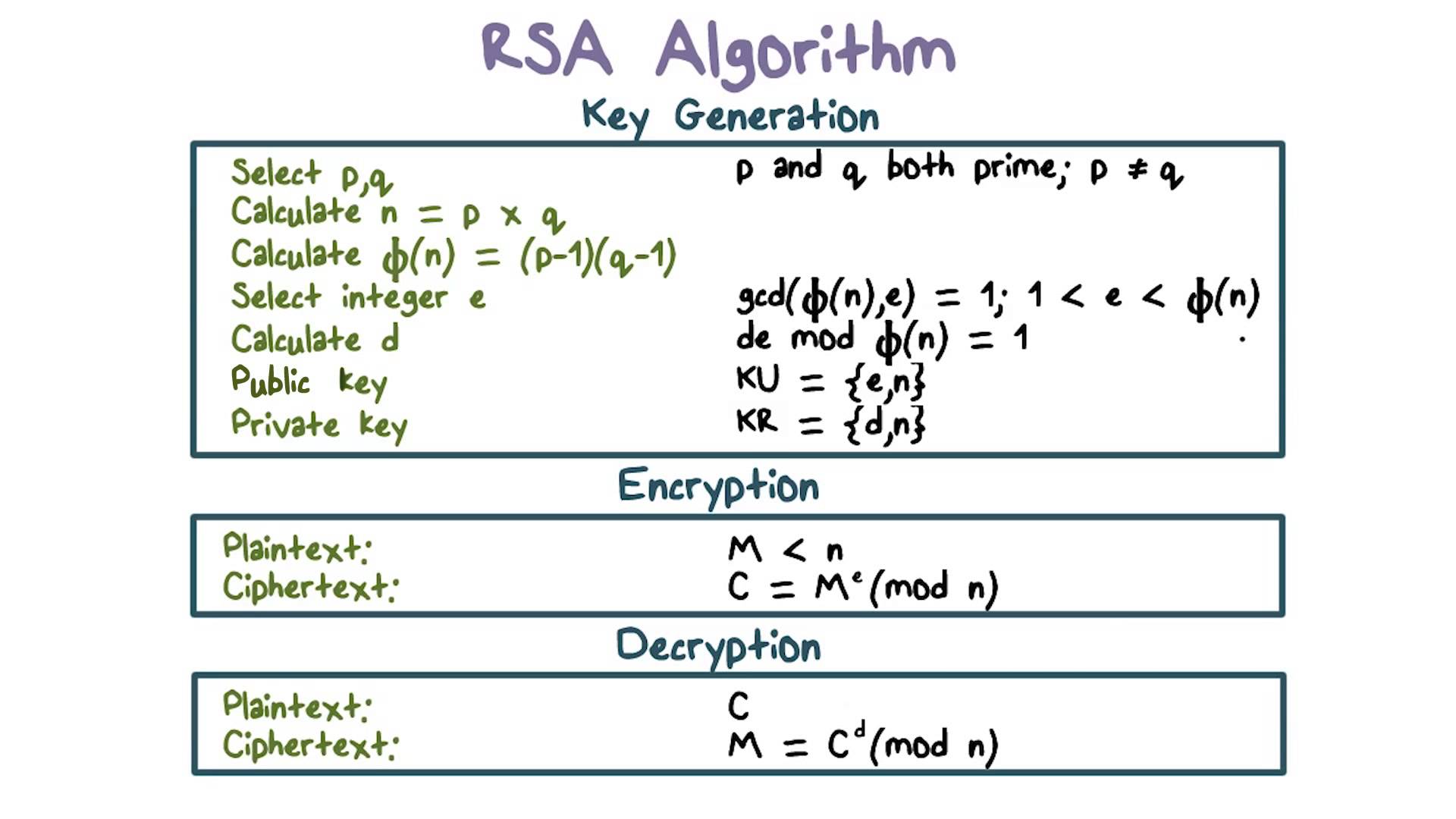
- Key Generation:Two large prime numbers, pand q, are generated randomly. The product of pand qis denoted as n, which is the modulus. Two other numbers, eand d, are generated such that eis relatively prime to ( p-1)
- ( q-1) and dis the multiplicative inverse of emodulo ( p-1)
- ( q-1). The public key is ( n, e), and the private key is ( n, d).
- Encryption:To encrypt a message M, the sender uses the recipient’s public key ( n, e) to compute the ciphertext Cas follows: C= Memod n.
- Decryption:To decrypt the ciphertext C, the recipient uses their private key ( n, d) to compute the original message Mas follows: M= Cdmod n.
For example, consider the following RSA parameters:
- p= 3
- q= 11
- n= p– q= 33
- e= 7
- d= 3
To encrypt the message M= 5, the sender computes the ciphertext Cas follows:
C= Memod n= 5 7mod 33 = 27
To decrypt the ciphertext C= 27, the recipient computes the original message Mas follows:
M= Cdmod n= 27 3mod 33 = 5
RSA Encryption Calculator Features
RSA encryption calculators are online tools that make it easy to encrypt and decrypt messages using the RSA encryption algorithm. They are typically free to use and can be found on a variety of websites.
Here are some of the key features of an RSA encryption calculator:
- Encryption:RSA encryption calculators can be used to encrypt messages using the RSA encryption algorithm. This algorithm is based on the difficulty of factoring large numbers, and it is considered to be one of the most secure encryption algorithms available.
- Decryption:RSA encryption calculators can also be used to decrypt messages that have been encrypted using the RSA encryption algorithm. This requires the use of the private key that was used to encrypt the message.
- Key generation:Some RSA encryption calculators can also be used to generate RSA key pairs. This is the first step in using the RSA encryption algorithm, and it is important to generate a key pair that is strong enough to resist attack.
Using an RSA Encryption Calculator
Using an RSA encryption calculator is simple. Typically, you will need to provide the following information:
- The message you want to encrypt or decrypt
- The public key of the recipient (for encryption) or the private key of the sender (for decryption)
Once you have provided this information, the calculator will perform the encryption or decryption process. The output will be the encrypted or decrypted message.
Comparison of RSA Encryption Calculators
There are a number of different RSA encryption calculators available online. Some of the most popular calculators include:
- RSA Labs’ RSA Calculator
- Cryptii’s RSA Encryptor/Decryptor
- DCode’s RSA Encryption/Decryption Tool
These calculators all offer similar features, but they may differ in terms of ease of use, speed, and security. It is important to choose a calculator that meets your specific needs.
Applications of RSA Encryption
RSA encryption, known for its robust security, finds applications in various domains, including secure communication protocols and real-world scenarios.
In secure communication protocols, RSA encryption plays a crucial role in:
- Establishing secure connections:RSA is used in protocols like TLS/SSL to create encrypted channels for secure data exchange between clients and servers.
- Digital signatures:RSA is employed to create digital signatures that authenticate the sender and ensure message integrity during electronic transactions.
Real-World Applications
Beyond communication protocols, RSA encryption has practical applications in:
- E-commerce transactions:RSA secures online payments by encrypting sensitive financial data during transactions.
- Software protection:RSA encryption is used to protect software from unauthorized distribution and modification.
- Blockchain technology:RSA encryption is employed in blockchain networks to secure digital assets and transactions.
RSA Encryption Security Considerations
RSA encryption, like any cryptographic algorithm, has certain security considerations that must be taken into account to ensure the integrity and confidentiality of encrypted data.
One of the primary concerns with RSA encryption is the key length. The security of RSA encryption relies heavily on the size of the keys used. Longer keys provide stronger encryption and make it more difficult for attackers to break the encryption.
However, longer keys also require more computational resources to generate and use, which can impact performance.
Another security consideration is the potential for side-channel attacks. Side-channel attacks are a type of attack that exploits information leaked from the implementation of a cryptographic algorithm. For example, an attacker could use timing attacks to determine the secret key used for RSA encryption.
To use RSA encryption securely, it is important to follow best practices. These include using strong key lengths, implementing countermeasures against side-channel attacks, and regularly updating the encryption algorithm and implementation to address any newly discovered vulnerabilities.
Key Length
The key length is one of the most important factors in determining the security of RSA encryption. Longer keys provide stronger encryption, but they also require more computational resources to generate and use. The recommended key length for RSA encryption is at least 2048 bits.
However, for applications that require the highest level of security, key lengths of 4096 bits or more may be used.
Side-Channel Attacks, Rsa encryption calculator
Side-channel attacks are a type of attack that exploits information leaked from the implementation of a cryptographic algorithm. For example, an attacker could use timing attacks to determine the secret key used for RSA encryption. To protect against side-channel attacks, it is important to use countermeasures such as constant-time implementations and blinding techniques.
Best Practices
To use RSA encryption securely, it is important to follow best practices. These include:
- Using strong key lengths
- Implementing countermeasures against side-channel attacks
- Regularly updating the encryption algorithm and implementation to address any newly discovered vulnerabilities
Final Summary
As we conclude our exploration of RSA encryption, it is evident that this cryptographic marvel continues to play a pivotal role in safeguarding our digital realm. Its versatility and adaptability make it an invaluable asset for securing communication channels, protecting sensitive information, and upholding the integrity of our online transactions.
Remember, the strength of RSA encryption lies not only in its mathematical foundations but also in its proper implementation and usage. By adhering to best practices and staying abreast of emerging threats, we can harness the full potential of this encryption technique to safeguard our digital communications and protect our privacy in the ever-evolving landscape of cybersecurity.
