Welcome to the realm of Linux permissions, where the Linux permissions calculator takes center stage as our trusty guide. This indispensable tool empowers us to navigate the complexities of file and directory access, ensuring data security and system integrity. Join us as we delve into the intricacies of Linux file permissions, unraveling their significance and exploring the myriad ways to manage them effectively.
Linux file permissions are the gatekeepers of your system, determining who can access, modify, or delete files and directories. Understanding and managing these permissions is paramount for maintaining a secure and well-organized computing environment. With the Linux permissions calculator at our disposal, we can simplify this task, ensuring that our files are protected and our system remains secure.
File Permissions Calculator

A file permissions calculator is a tool that helps you determine the permissions for a file or directory. It can be used to check the permissions of existing files or directories, or to calculate the permissions that you need to set for a new file or directory.
To use a file permissions calculator, you simply enter the name of the file or directory that you want to check, and the calculator will display the permissions for that file or directory. You can also enter a specific set of permissions that you want to calculate, and the calculator will tell you what the resulting permissions will be.
Benefits of Using a File Permissions Calculator
- File permissions calculators can help you to ensure that your files and directories are properly secured.
- They can also help you to troubleshoot problems with file permissions.
- File permissions calculators are easy to use and can save you time and effort.
Understanding Linux File Permissions
Linux file permissions are a fundamental concept in understanding how the operating system controls access to files and directories. They determine who can read, write, and execute files, ensuring the security and integrity of the system.
Types of Linux File Permissions
Linux file permissions are divided into three categories: user permissions, group permissions, and other permissions.
- User permissionscontrol the access rights of the file’s owner.
- Group permissionscontrol the access rights of the group to which the file belongs.
- Other permissionscontrol the access rights of all other users on the system.
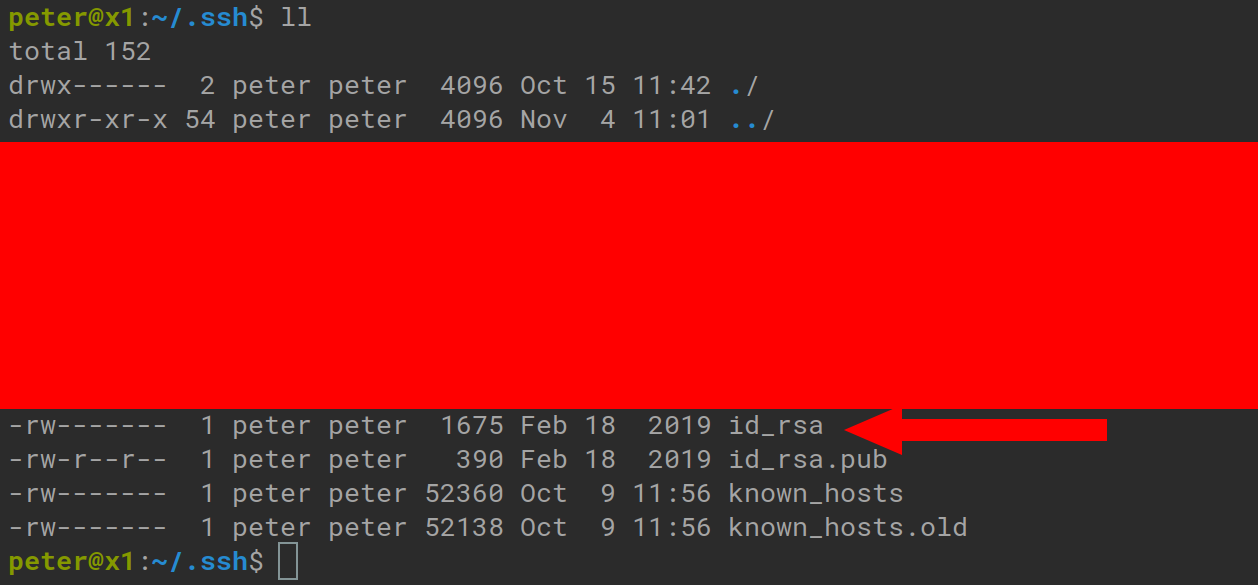
Reading and Interpreting Linux File Permissions
Linux file permissions are represented as a string of three characters, each representing the permissions for one of the three categories. The characters are:
- r: read permission
- w: write permission
- x: execute permission
If a character is replaced by a dash (-), it indicates that the corresponding permission is not granted.
Common Linux File Permissions
Here are some common Linux file permissions and their meanings:
- -rw-r–r–: The file is readable and writable by the owner, readable by the group, and readable by others.
- -rwxr-xr-x: The file is readable, writable, and executable by the owner, readable and executable by the group, and readable and executable by others.
- drwxr-xr-x: The file is a directory that is readable, writable, and executable by the owner, readable and executable by the group, and readable and executable by others.
Managing File Permissions: Linux Permissions Calculator

Managing file permissions in Linux is crucial for ensuring the security and integrity of your system. Various methods exist to manage file permissions effectively, each with its own advantages and implications.
Using the chmod Command
The chmodcommand allows you to modify file permissions by specifying the desired permissions and the target file. It accepts three arguments: the permission flags, the user/group specification, and the target file. Permission flags include r(read), w(write), and x(execute), while user/group specification can be u(user), g(group), o(others), or a(all).
For example, to grant write permission to the user and read permission to others for the file myfile, you would use:
chmod u+w,o+r myfile
Using the chown Command
The chowncommand is used to change the owner or group ownership of a file. It takes two arguments: the new owner/group and the target file. The owner/group can be specified using the username or group name.
For instance, to change the owner of myfileto john, you would use:
chown john myfile
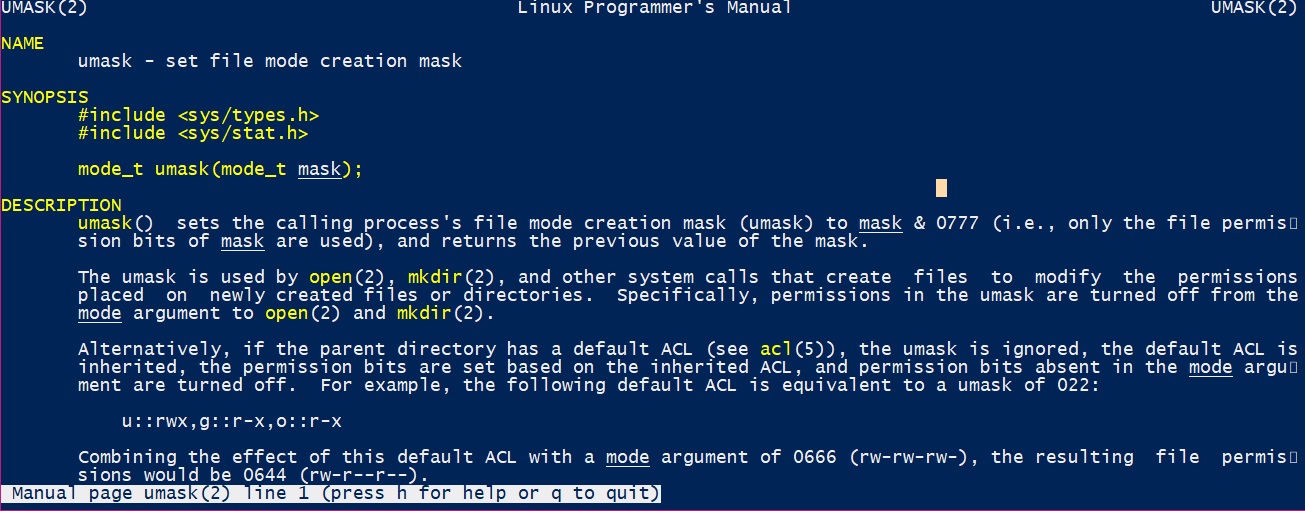
Using the umask Command
The umaskcommand sets the default file permissions for newly created files. It takes a three-digit octal number as an argument, representing the permissions to be denied for the user, group, and others.
For example, to set the default file permissions to 644(read/write for user, read-only for group and others), you would use:
umask 022
Security Implications, Linux permissions calculator
Managing file permissions has significant security implications. Incorrect permissions can allow unauthorized users to access, modify, or delete sensitive files. It is essential to understand the different permissions and their impact on system security.
For instance, granting write permission to others for a confidential file could compromise its integrity. Similarly, allowing execute permission to a script could potentially lead to malicious code execution.
Therefore, it is crucial to carefully consider the permissions granted to files and ensure that they align with the desired level of access and security requirements.
Advanced File Permissions Management
Advanced file permissions management techniques extend beyond basic user, group, and other permissions. These techniques provide granular control over file access, enabling system administrators to implement sophisticated security measures.
One advanced technique is Access Control Lists (ACLs). ACLs allow the assignment of specific permissions to individual users or groups, even if they are not the file’s owner or members of the file’s group. This enables precise control over file access, ensuring that only authorized individuals have the necessary permissions.
Extended Attributes
Extended attributes provide a mechanism to store additional metadata about files, including security-related information. By leveraging extended attributes, system administrators can define custom permissions or security policies that are not supported by traditional file permissions.
Benefits of Advanced File Permissions Management
- Enhanced security: ACLs and extended attributes provide finer-grained control over file access, reducing the risk of unauthorized access.
- Improved compliance: Advanced file permissions management techniques facilitate compliance with regulatory requirements and industry best practices.
- Increased flexibility: ACLs and extended attributes allow for the implementation of complex security policies that are tailored to specific business needs.
Limitations of Advanced File Permissions Management
- Complexity: Managing ACLs and extended attributes can be complex, requiring specialized knowledge and tools.
- Compatibility: ACLs and extended attributes may not be supported by all file systems or operating systems.
- Performance overhead: Implementing advanced file permissions management techniques can introduce a performance overhead, especially in environments with a large number of files.
Closure
In the ever-evolving digital landscape, understanding and managing Linux file permissions has become a cornerstone of system security and data protection. The Linux permissions calculator serves as an invaluable ally in this endeavor, empowering us to navigate the complexities of file access with confidence and precision.
As we conclude our exploration, remember that the security of your system lies in your hands. Embrace the power of the Linux permissions calculator and safeguard your data with the utmost care.
